These obligations can be covered by appropriate use of technology, but only once the underlying business needs have been appraised. A first step is an information audit, as described in a previous article in this series, upon which risk assessments and mitigation plans can be created.
Risk assessment
Step 1: Three important questions
A good place to start with risk analysis is to look at each type of information identified in the information audit with three questions in mind:
1. Event: What might happen to this information? Think about how the information is stored. Could it be lost or destroyed in its current form (is paper at risk of fire or flood; could electronic files be lost if the server crashes)? How might the information 'leak' out of the organisation (theft, USB stick loss, unauthorised disclosure, e-mail to the wrong person)? This question should identify a number of risks against each specific piece of information.
2. Probability: How likely is this to actually happen? For example, a fire is a fairly unlikely risk. However, if you store data on USB disks, it is fairly likely that someone will lose one.
3. Impact: What would be the impact? Some risks have bigger impacts than others. If you can’t locate a permission slip, then you can ask for another to be created – a low impact event. However, if someone has left an SEN file on the bus, that’s a serious problem.
Step 2: Plot your risk priorities
When you have this information, categorise each event by its probability and impact (low, medium or high) and plot each event onto a grid with probability on the x-axis and impact on the y-axis. Key issues will appear in the top-right, giving you a good appreciation of your risk priorities and where to start.
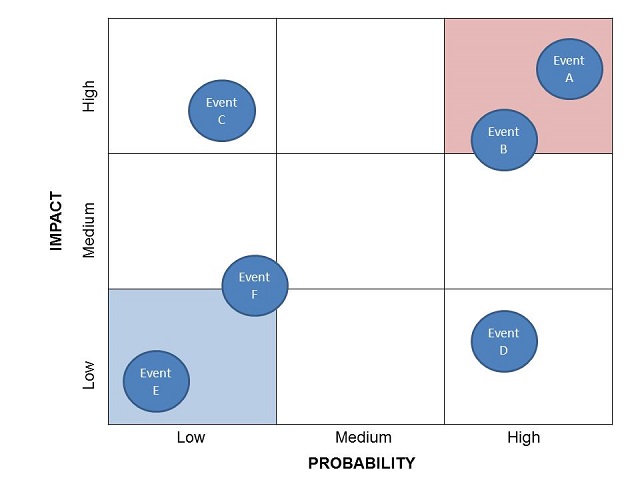
Take care not to neglect events which may be unlikely but would have a very serious impact; these “Black Swan” events will still need some thought, prevention and possibly even a coping strategy.
Step 3: Mitigation plans
The next step is to consider risk mitigation – what can you do about some of these risks to reduce their impact or remove them altogether?
The IRMS toolkit describes a number of mitigations to general IT risks including off-site and secure backups, password policies and having no fragile or sensitive data stored on local PCs or laptops. This is all essential.
The Toolkit also discusses the risks associated with loss of paper documents in a flood or fire and the benefits of metal cabinets over open shelves, as well as the need for auditing of paper file locations and clear desk policies. These are, again, all essential if using paper files – but these steps only mitigate the risks, rather than removing them.
The application of an appropriate Electronic Document Management System (EDMS) can remove the risks to physical paperwork, by removing it, and placing the information archive into the protection of IT mitigation procedures. If this is done, information stores such as pupil files are covered by the same processes and policies as any other IT backup – greatly reducing risks and saving time by covering a multitude of risks together. An EDMS can also provide access security and auditing, thereby removing many information leakage risks.
Continuity planning
Having undertaken a risk management exercise, determined impacts and mitigated as much as possible, the next step is to compile a list of actions which will be taken should the worst happen – and in what timeframes.
Again, this builds on the information audit and the key question is how quickly does each classification of information need to be made available again? Once this is understood, the order of restoring IT systems (typically) can be defined – and then this should be subject to some real-world thinking as to whether it is practical. For example, if a file server contains information which is required to be made available within 24 hours of a server failure, can the backup be restored to a spare server or does a new server need to be procured?
If a new server is required – maybe the spare server is also likely to be destroyed? – then there needs to be a plan for how this will be achieved to meet the overall elapsed time requirement.
Test, test and test again…
A continuity plan is something you hope never to need. But it must be tested – and that testing should be regularly repeated. Without testing, you have no assurance that the plan is complete, actionable and up-to-date. This can be a painful and time-consuming process but it’s just not possible to write a plan which is error-free, and you don’t want to meet the problems when you are already in the midst of a crisis.
When the worst happens
Sadly, we have seen cases where large amounts of paper documents have been lost. Examples include fires destroying buildings used for information storage, floods wiping out basement archives and even leaky roofs causing irreparable damage. We’ve also seen a surprising number of servers lost without an up-to-date backup being available. In most of these cases, a major impact has been suffered because a thorough risk assessment and/or regular process checking were not done. Having said this, some events were acknowledged as low-probability/high-impact risks against which the organisation had taken a conscious and calculated risk.
The IRMS toolkit states that an individual should be appointed as the "named member of staff to liaise with the Information Commissioner’s Office in the event that a major information breach needs to be reported". We hope that by following these guidelines, and by using appropriate technology, this named person will have no need to speak to the ICO!
This concludes the series on the IRMS toolkit for schools, we hope you’ve enjoyed these articles and if you have any questions please do get in touch.